CCNA 5.0 (CCNA R&S) – Connecting Networks Final Exam P2
31
Which two statements about DSL are true? (Choose two.)
users are on a shared medium
uses RF signal transmission
local loop can be up to 3.5 miles (5.5km)
physical and data link layers are defined by DOCSIS
user connections are aggregated at a DSLAM located at the CO
32
Which IEEE standard defines the WiMax technology?
802.3
802.5
802.11
802.16
33
Which broadband technology would be best for a small office that requires fast upstream connections?
DSL
fiber-to-the-home
cable
WiMax
34
Which broadband solution is appropriate for a home user who needs a wired connection not limited by distance?
cable
DSL
WiMax
ADSL
35
Which technology requires the use of PPPoE to provide PPP connections to customers?
dialup analog modem
dialup ISDN modem
DSL
T1
36
What is the expected behavior of an ADSL service?
The download rate is faster than the upload rate.
The upload rate is faster than the download rate.
The download and upload rates are the same.
The user can select the upload and download rates based on need.
37
What is a type of VPN that is generally transparent to the end user?
site-to-site
remote access
public
private
38
Which two statements describe remote access VPNs? (Choose two.)
Remote access VPNs are used to connect entire networks, such as a branch office to headquarters.
End users are not aware that VPNs exists.
A leased line is required to implement remote access VPNs.
Client software is usually required to be able to access the network.
Remote access VPNs support the needs of telecommuters and mobile users.
39
What are three characteristics of the generic routing encapsulation (GRE) protocol? (Choose three.)
GRE tunnels support multicast traffic.
By default, GRE does not include any flow control mechanisms.
Developed by the IETF, GRE is a secure tunneling protocol that was designed for Cisco routers.
GRE uses AES for encryption unless otherwise specified.
GRE creates additional overhead for packets that are traveling through the VPN.
GRE provides encapsulation for a single protocol type that is traveling through the VPN.
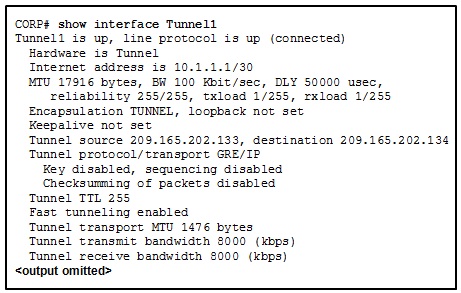
40
Refer to the exhibit. Which IP address is configured on the physical interface of the CORP router?
10.1.1.1
10.1.1.2
209.165.202.133
209.165.202.134
41
Which algorithm is considered insecure for use in IPsec encryption?
3DES
AES
RSA
SHA-1
42
Which two statements correctly describe asymmetric encryption used with an IPsec VPN? (Choose two.)
Encryption and decryption use a different key.
AES is an example of an asymmetric encryption protocol.
Public key encryption is a type of asymmetric encryption.
A shared secret key is used to perform encryption and decryption.
The same encryption keys must be manually configured on each device.
43
What is the purpose of a message hash in a VPN connection?
It ensures that the data cannot be read in plain text.
It ensures that the data has not changed while in transit.
It ensures that the data is coming from the correct source.
It ensures that the data cannot be duplicated and replayed to the destination.
44
What is required for a host to use an SSL VPN to connect to a remote network device?
VPN client software must be installed.
A site-to-site VPN must be preconfigured.
A web browser must be installed on the host.
The host must be connected to a wired network.
45
What is the default location for Cisco routers and switches to send critical logging events?
auxiliary port
console port
syslog server
virtual terminal
46
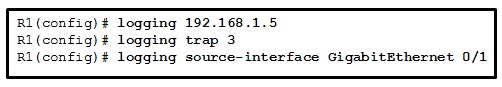
Refer to the exhibit. Which three events will occur as a result of the configuration shown on R1? (Choose three.)
Messages that are sent to the syslog server will be limited to levels 3 or lower.
Messages that are sent to the syslog server will be limited to levels 3 and higher.
Only traffic that originates from the GigabitEthernet 0/1 interface will be monitored.
Messages that are sent to the syslog server will use 192.168.1.5 as the destination IP address.
The syslog messages will contain the IP address the GigabitEthernet 0/1 interface.
For multiple occurrences of the same error, only the first three messages will be sent to the server.
47
Which statement is a characteristic of SNMP MIBs?
The MIB organizes variables in a flat manner.
The SNMP agent uses the SNMP manager to access information within the MIB.
The NMS must have access to the MIB in order for SNMP to operate properly.
The MIB structure for a given device includes only variables that are specific to that device or vendor.
48
Which SNMP message type informs the network management system (NMS) immediately of certain specified events?
GET request
SET request
GET response
Trap
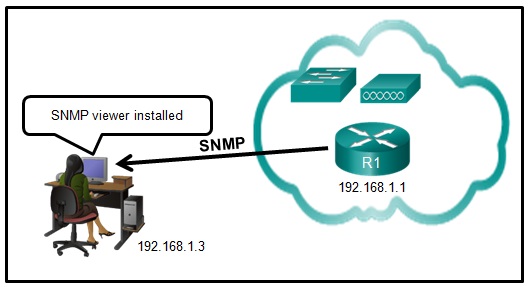
49
Refer to the exhibit. Router R1 was configured by a network administrator to use SNMP version 2. The following commands were issued:
R1(config)# snmp-server community batonaug ro SNMP_ACL
R1(config)# snmp-server contact Wayne World
R1(config)# snmp-server host 192.168.1.3 version 2c batonaug
R1(config)# ip access-list standard SNMP_ACL
R1(config-std-nacl)# permit 192.168.10.3
Why is the administrator not able to get any information from R1?
The snmp-server enable traps command is missing.
The snmp-server community command needs to include the rw keyword.
There is a problem with the ACL configuration.
The snmp-server location command is missing.
50
In the data gathering process, which type of device will listen for traffic, but only gather traffic statistics?
NMS
syslog server
NetFlow collector
SNMP agent
51
What type of information is collected by Cisco NetFlow?
interface errors
CPU usage
memory usage
traffic statistics
52
Which three flows associated with consumer applications are supported by NetFlow collectors? (Choose three.)
bandwidth regulation
accounting
billing
quality of service
error correction
network monitoring
53
Users are reporting longer delays in authentication and in accessing network resources during certain time periods of the week. What kind of information should network engineers check to find out if this situation is part of a normal network behavior?
syslog records and messages
the network performance baseline
debug output and packet captures
network configuration files
54
Which two specialized troubleshooting tools can monitor the amount of traffic that passes through a switch? (Choose two.)
TDR
digital multimeter
NAM
portable network analyzer
DTX cable analyzer
55
What are two examples of network problems that are found at the data link layer? (Choose two.)
encapsulation errors
framing errors
electromagnetic interference
incorrect interface clock rates
late collisions and jabber
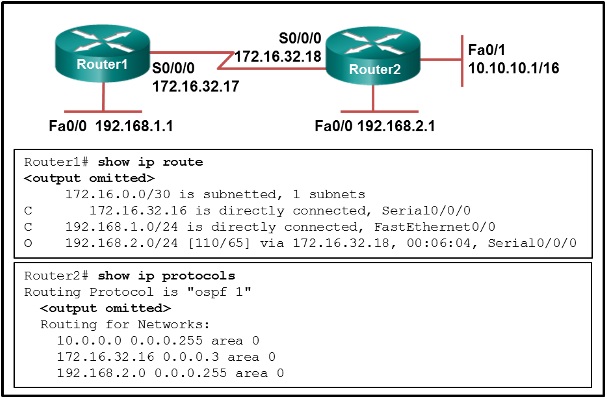
56
Refer to the exhibit. A network administrator is troubleshooting the OSPF network. The 10.10.0.0/16 network is not showing up in the routing table of Router1. What is the probable cause of this problem?
The serial interface on Router2 is down.
The OSPF process is not running on Router2.
The OSPF process is configured incorrectly on Router1.
There is an incorrect wildcard mask statement for network 10.10.0.0/16 on Router2.
57
A group of Windows PCs in a new subnet has been added to an Ethernet network. When testing the connectivity, a technician finds that these PCs can access local network resources but not the Internet resources. To troubleshoot the problem, the technician wants to initially confirm the IP address and DNS configurations on the PCs, and also verify connectivity to the local router. Which three Windows CLI commands and utilities will provide the necessary information? (Choose three.)
arp -a
ipconfig
nslookup
ping
telnet
tracert
netsh interface ipv6 show neighbor
58
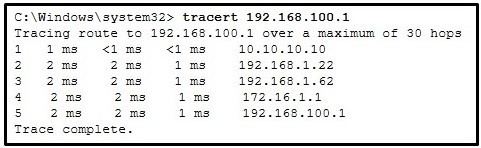
Refer to the exhibit. On the basis of the output, which two statements about network connectivity are correct? (Choose two.)
There is connectivity between this device and the device at 192.168.100.1.
The connectivity between these two hosts allows for videoconferencing calls.
There are 4 hops between this device and the device at 192.168.100.1.
The average transmission time between the two hosts is 2 miliseconds.
This host does not have a default gateway configured.
59
60
31-3,5
32-4
33-2
34-1
35-3
36-1
37-1
38-4,5
39-1,2,5
40-3
41-1
42-1,3
43-2
44-3
45-2
46-1,4,5
47-3
48-4
49-3
50-3
51-4
52-2,3,6
53-2
54-3,4
55-1,2
56-4
57-2,3,4
58-1,3
59